Access ssh without password, I think it’s one of the things, most useful for anyone who has to deal with multiple servers at the same time, especially for those who need to make copies of files between them.
DSA is an acronym for Digital Signature Standard (Digital Signature Standart), created by NIST, and specifies the digital signature for DSA and SHA-1 for hashing. The DSA is an asymmetric algorithm and the private key operates on the hash SHA-1. To verify the signature piece of code calculates the hash piece and another uses the public key to decrypt the signature, and finally comparing the results of both ensuring the author of the message. The DSA works with keys of 512 to 1024 bits, but unlike the RSA which is multipurpose, DSA ??signs only and does not guarantee confidentiality. Another against DSA is that the generation of the signature is faster than RSA, but 10 to 40 times slower to check the signature.
How does ssh-keygen?
The ssh-keygen , raises public and private keys, so that from them if you can access the server. Which in our case will occur without typing the password, but this key usage is as a hint, to improve the security of access to the server, of course, if using with password.
Hands on mass
Open your terminal, call your grandmother, and the whole family to watch.
Generating the keys
It is up to you which encryption use, so I made the explanation of the two. Since you’re with your family, make a poll to decide which is the best. After the vote, follow the tutorial, I’ll use the rsa, if uses dsa, just change where rsa, dsa.
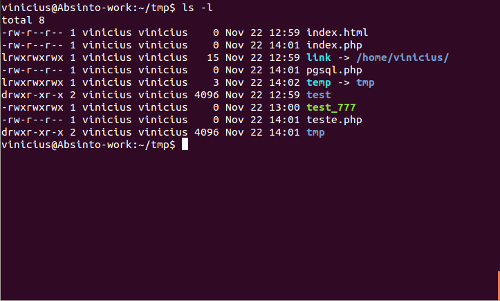
log in to terminal, with the user that you want to access the server without password. Because the key is specific to the user.
ssh-keygen-t rsa
You will get the following response:
Generating public/private rsa key pair.
Enter file in which to save the key (/home/vinicius/.ssh/id_rsa):
My user is vinicius, I don’t know if you’ve noticed, but my name is that (see the url!).Finally, choose the folder in which to save the key. If ta with laziness only confirms.And you will receive another message.This step is very important
Enter passphrase (empty for no passphrase):
As you read above, enter the password (the password). As we want to access without password, only, confirm (press enter, ask your grandmother!) without typing anything.He will ask for confirmation, press “enter” again. Confirmation:
Enter same passphrase again:
Ready, created the key.
Your identification has been saved in/home/vinicius/.ssh/id_rsa.
Your public key has been saved in/home/vinicius/.ssh/id_rsa.pub.
The key fingerprint is ...
It generates a lot of cute character, that are not suitable to put in this post. Everything created, now we put the public key on the server, to which we want to access without password.
Putting the public key in the destination server.
There are a few different ways to do this step, even found a very interesting when writing this post. I will describe two, a simple, and another simpler still.
Simple mode
What must be done is to put the contents of the public key (id_rsa.pub) on the server, specifically the file authorized_keys in either user, the server, to which we have access.
Let’s assume that the user name is joao, on the server viniciusmuniz.com
First let’s copy the public key to the server
/home/vinicius/.ssh/id_rsa.pub scp joao@viniciusmuniz.com:/home/joao/
enter their password, their penultimate time to type it. And then access the server, and place the public key in the authorized_keys
ssh joao@viniciusmuniz.com
cat/home/joao/id_rsa.pub > >/home/joao/.ssh/authorized_keys
Ready! Now test the ssh access, that there will be no further need for password.
Super simple mode
This way I found writing this post. There is a facility that is the ssh-copy-id , which with just one command, he inserts the public key in the destination server.
ssh-copy-id -i /home/vinicius/.ssh/id_rsa.pub joao@viniciusmuniz.com
Accessing ssh without password
Now just login, there will be no more need for password. Join the fun!
ssh joao@viniciusmuniz.com








Recent Comments