Permissions on Linux, is the main "feature" of Unix-based systems. They are used in different ways and for different purposes. But mostly for safety and organization of a system.
Through the permissions, you can define who can access, write and execute a file. Any per group, or per-user. With permissions, Linux prevents a malicious program, for example, delete a file that should not send special files to someone else or provide network access for other users to invade the system.
Let us understand better, and learn how to change and check the permissions of certain directory or file.
Checking permission
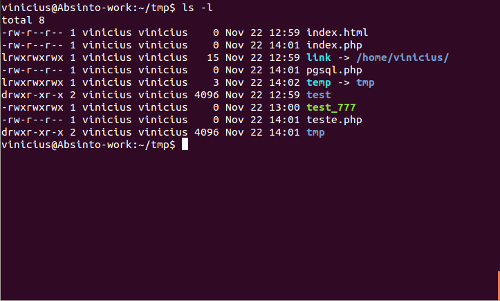
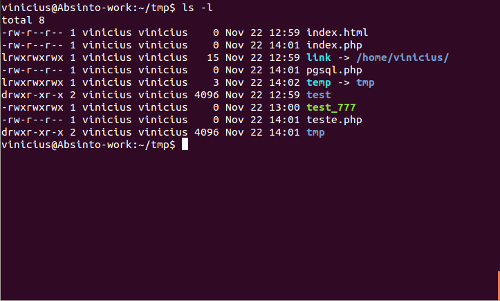
To check the permissions of a file or directory, it is common to use the command ls with parameter -l , it’s will discover with the permissions and owners of files and directories .
ls -l /home/vinicius/tmp/
Returns me the result:
total 4
-Rw-r - r - 1 vinicius vinicius 0 Nov 22 12:59 index.html
lrwxrwxrwx 1 vinicius vinicius 15 Nov 22 12:59 link -> / home / vinicius /
drwxr-xr-x 2 vinicius vinicius 4096 Nov 22 24:59 test
-Rwxrwxrwx 1 vinicius vinicius 0 Nov 22 13:00 test_777
Okay? Ta thinking this is a lot of loose letter right? Let us understand what each part of it means.
directory, link, file?
To know what each item is, just look at the first letter.
- l => means that this item is a link;
- d => That item is a directory;
- – => A file;
- b => block file;
- c => character special file;
- p => channel;
- s => socket;
rwx what’s this?
You noticed that these letters are being repeated throughout the list of ls, each has its meaning:
- r => read – indicates read permission;
- w => write – indicates writable;
- x => Execution – indicates execution permission
- – => indicates no permission
Ready now know the meaning of each letter, we can now interpret the results of ls command. We can divide the result into 3 parts, let's take the first line as an example:
rw- | r - | r -
Each group of 3 characters means this order, the permission for the owner, permissions for the group that owns the file owner and permissions to other users.
Reading data only allowed -rw-r – r – , we can identify that a file is that the file owner has read and write permission, and that the other ( group and others) allowed only read.
Permission Bits
Each letter has its corresponding bit, which can be identified as follows:
| Lyrics |
Binary |
Decimal |
Meaning |
| — |
000 |
0 |
No permission |
| – x |
001 |
1 |
Execute permission |
| -w- |
010 |
2 |
Permission writing |
| wx |
011 |
3 |
write and execute permission |
| r – |
100 |
4 |
Read Permission |
| rx |
101 |
5 |
Readable and execution |
| rw- |
110 |
6 |
Permission reading and writing |
| rwx |
111 |
7 |
All permissions |
Changing permission
Using the above table if we can change the permission of files and directories with the chmod.
The syntax of the command chmod:
chmod
Some examples:
Full permission
chmod 777 test.txt
Permission read-only
chmod 444 test.txt
Permission reading and writing to the owner, read for others
chmod 644 test.txt
besides using chmod permissions with numbers , there is also possibility to use the most boring form of letters . Where we need to understand that
- u => user;
- g => group;
- O => other;
- a => all;
- + => add permission
- – => remove permission
- = => set the permission
With this we can use the chmod as follows :
Execute permission for the user
chmod u + x test.txt
Read permission for the group
chmod g+ r test.txt
The danger of allowing 777
As I said earlier , the permission 777 is the full permission to something , ie everyone can edit, delete , write . Imagine a file with permission 777 where everyone can edit it , someone with malicious intentions can edit your file , and run it , you can steal valuable information , run something on your operating system and erase data . So it is normal if you use permission 755 for directories and 644 for non-executable files such as php files on hosting servers .
Even this is something that some servers block with suPHP , whenever you have getting error 403 , first check the permissions of your files and folders , as in 90% of cases the problem is this .
You can understand more about it at:
http://www.guiafoca.org/cgs/guia/intermediario/ch-perm.html
CHMOD Wikipedia






Recent Comments